Being a professional developer for 24 years you pick up a few tools on the way, tools that help the development process, I got used to some of the tools, that I’m not planning to replace them, even if the competition is better.
I’m a C++ developer, and lately, I’ve been doing some PHP, so this list is geared mostly at C++, it’s possible that if I were a Java or Python programmer, the list would have been different.
I’m using Visual Studio for Windows, and GCC for Linux. I don’t think those tools need any introduction or review, so I’ll dive into the other tools I use.
Programming add-ons
Programming add-ons are plugins for Visual Studio that helps you write code, make your writing more efficient.
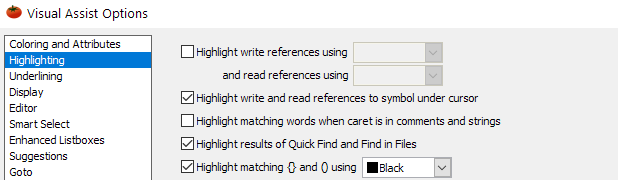
Visual Assist
I work with Visual Assist for 16 years, and this is my number one tool. I use it mostly for navigating between functions define and implementation, the dropdown options when selecting variables and switching between .cpp file and .h file, and finding references to who calls a function.
It’s possible that Visual Studio already does it all, doesn’t matter to me, I work with them.
Pros:
- Works on all Visual Studio versions
- Fair pricing
Cons:
- If working on unsupported language (for example PHP), then copy-paste log is not available
Build tools
Build tools are tools that help the build process, I used to build 50-100 versions at a time, each version with different Visual Studio, different features and I needed a software to help me manage it.
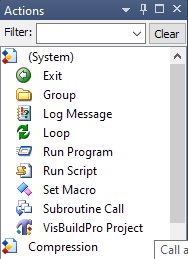
Visual Build
Visual build is a software that is used to build scripts; in my case, it was build scripts. It’s drag and drop and supports most development tools. It also allows to download files, do file manipulation. It contains VB script support and some limited programming.
For me, I couldn’t manage the build process without it.
Pros:
- Flexible
- Easy to use
Cons:
- May forced to buy an upgrade for new VS version
File editing tool
Sometimes you need to inspect files, may it be your input or output, and sometimes Notepad++ or Notepad just don’t cut it.
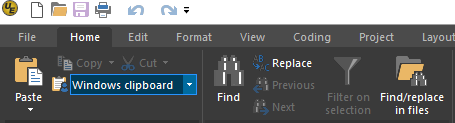
Ultraedit
Ultraedit offers an editor that can open big files, and since I have to inspect big files over 1G, I need special software to do it. Ultraedit has more features, and I don’t use any of them.
Pros:
- Can open big files
Cons:
- Crashes a lot
- Slow
HDD Hex Editor Neo
HDD Hex Editor Neo is a software to inspect and edit hex files, it has a free and paid version, and it’s easy to use. I don’t use it often, but when I need it, I need it.
Pros:
- Has a free version
- Easy to use
Cons:
- Sometimes search selection is messed up and needs to restart the app
Source control
Source control is a must for any programmer, or programming team, on top of being a backup it allows to diff files to see what changed, this is especially helpful to track new bugs that weren’t around in the previous version.
Vault
The first source control I used was Visual Source Safe, which at the time was unreliable. Here comes Vault to the rescue; it has the same interface, but is very reliable. I know Microsoft has fixed their source control with Team Foundation, but I already have a solution.
Also, I was never a fan of Git, so I’m pleased with this.
Pros:
- Reliable
- Has a free version
Cons:
- Backend/Frontend are Windows-based
- SQLServer backend
Virtual machine
When I developed apps, I had to test them on various Windows flavours. Also, I had to revert the machine after each install to make sure I start fresh.
VMWare Workstation
VMWare Workstation is a desktop virtualization tools that enabled to install most operating systems that will work in parallel with the current OS. Each OS is isolated from the main OS, which adds to security.
I tried to use some free similar apps, but it’s just not the same.
Pros:
- Reliable
- Easy to use
Cons:
- Needs to buy an upgrade license every two years
- Dropped support for old CPU
Writing tools
As a developer, you need to write documents, and it can be an email, a spec, or a blog post just like this. Today basic spelling test just doesn’t cut it.
Grammarly
Grammarly is an add-on to Word, Chrome and Outlook that allows you to refine your writing, after setting the goal it recommends how to improve/fix your writing. The add-on inspects each word in the context of the paragraphs, and that’s the way it beats traditional spell checker.
Pros:
- Easy to use
- Has many add-ons
Cons:
- Has mistakes from time to time
- Check privacy policy
Proxies and VPNs
When developing a network app, you may want to test it from different locations and with different network quality to make sure that the app that works on the corporate LAN will work just as well with unreliable mobile connection.
The most significant difference between a proxy service and a VPN that with the proxy you get an IP and a port to connect to, with VPN it installs a client that automatically intercepts all your connections.
NordVPN
NordVPN is one of the leading VPN vendors, and it supports many locations and OS. Use the most remote location to test how your app handles latency and slower speeds.
Pros:
- Supports many locations
- Supports many OS
Cons:
- Cheaper options available
Storm Proxies
Storm proxies offer residential and data centre proxies since it uses a back connect method, which means you connect to a single server. It connects to the actual proxy, it can make the connection less stable, and it’s the perfect settings for your app.
Pros:
- Affordable
Cons:
- Old UI